Understanding how security measures like Antiviruses operate is crucial for defenders and those who aim to test system vulnerabilities. One intriguing method involves using AES (Advanced Encryption Standard) encryption alongside ISO files to bypass Mark-of-the-Web (MOTW) tagging, a feature designed to flag files downloaded from potentially unsafe internet sources. Here’s how this technique can be employed.
Understanding MOTW and Its Purpose
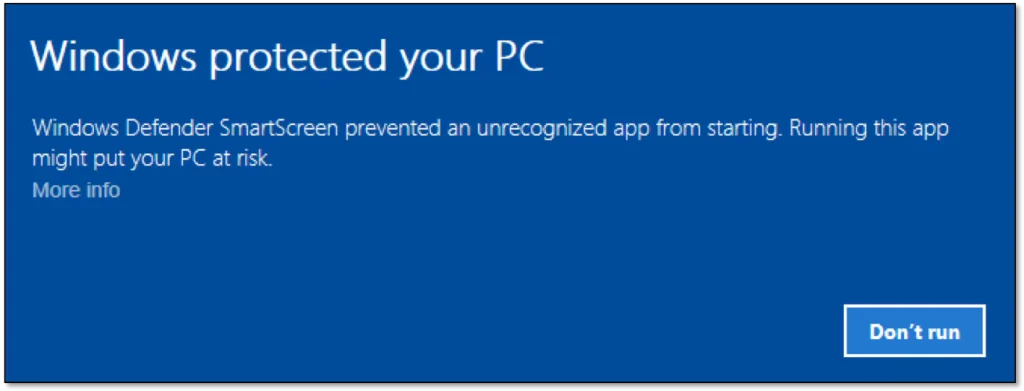
MOTW, or Mark-of-the-Web, is a security feature in Windows that tags files downloaded from the internet with an Alternate Data Stream (ADS) known as Zone.Identifier. This tag alerts users that a file might not be safe to open directly, often prompting additional security measures like running Office documents in Protected View or alerting users through SmartScreen when attempting to run executable files. The purpose is to prevent malware from executing without user awareness or consent.
The Role of AES Encryption
AES encryption is a symmetric block cipher endorsed by the U.S. government for securing sensitive, unclassified information. AES can be used with different key sizes (128-bit, 192-bit, or 256-bit), offering varying levels of security. For our context, AES encryption helps mask the content of potentially harmful files, making it difficult for antivirus or security software to identify them based on known malware signatures.
- Encryption: Before distribution, the malicious payload is encrypted using AES, rendering it unreadable to static antivirus scans.
- Decryption: Upon execution, the payload must be decrypted, which is where dynamic analysis could potentially detect it. However, this can be mitigated with clever implementation or further evasion techniques.
Using ISO Files to Evade MOTW
ISO files, which are disk image files, have been noted for their capability to bypass MOTW because they do not support NTFS alternate data streams where MOTW tags are stored:
- Container Strategy: By placing the encrypted payload inside an ISO file, the malware can be delivered without the MOTW flag. When a user mounts or extracts the ISO, the files within it are not marked as coming from the internet, thus bypassing the initial security warning.
- Execution: The user then needs to open or execute the file from this ISO, which might not trigger the same level of scrutiny as a directly downloaded file would.
Combining AES with ISO
Here’s how you might combine these techniques:
- Encrypt the Malware: Use AES to encrypt the malicious code or payload. This step ensures that static antivirus checks do not immediately identify the file as malicious.
- Pack into ISO: Embed the encrypted file into an ISO image. When the ISO is mounted or its contents are extracted, the files within do not carry the MOTW tag.
- User Interaction: The final step requires user action to execute the file from the ISO. This could be through a script or a document that, when opened, decrypts and runs the payload.
Security Implications
- Detection Challenges: This method complicates detection for security software, especially if combined with additional evasion tactics like living off the land binaries or abusing trusted system tools.
- Mitigation for Users: Users and organizations should be wary of ISO files, treating them with the same caution as downloaded executables. Enhanced monitoring for unusual file system activities and employing robust endpoint protection that looks beyond signatures could help.
Conclusion
While using AES encryption within ISO files to bypass MOTW is clever, it highlights the ongoing cat-and-mouse game in cybersecurity. Security professionals must keep evolving their detection and prevention strategies, while users should remain vigilant about any file they interact with, regardless of its origin or format.
Real Word Scenario
Recently, in one of our engagements, we came across Acronis Cyber Protect, where we utilized the techniques mentioned earlier to bypass it entirely.